mirror of https://github.com/go-gitea/gitea
Tag:
Branch:
Tree:
fe82991547
main
release/v1.10
release/v1.11
release/v1.12
release/v1.13
release/v1.14
release/v1.15
release/v1.16
release/v1.17
release/v1.18
release/v1.19
release/v1.20
release/v1.21
release/v1.22
release/v1.22-legacy
release/v1.8
release/v1.9
v0.9.99
v1.0.0
v1.0.1
v1.0.2
v1.1.0
v1.1.1
v1.1.2
v1.1.3
v1.1.4
v1.10.0
v1.10.0-dev
v1.10.0-rc1
v1.10.0-rc2
v1.10.1
v1.10.2
v1.10.3
v1.10.4
v1.10.5
v1.10.6
v1.11.0
v1.11.0-dev
v1.11.0-rc1
v1.11.0-rc2
v1.11.1
v1.11.2
v1.11.3
v1.11.4
v1.11.5
v1.11.6
v1.11.7
v1.11.8
v1.12.0
v1.12.0-dev
v1.12.0-rc1
v1.12.0-rc2
v1.12.1
v1.12.2
v1.12.3
v1.12.4
v1.12.5
v1.12.6
v1.13.0
v1.13.0-dev
v1.13.0-rc1
v1.13.0-rc2
v1.13.1
v1.13.2
v1.13.3
v1.13.4
v1.13.5
v1.13.6
v1.13.7
v1.14.0
v1.14.0-dev
v1.14.0-rc1
v1.14.0-rc2
v1.14.1
v1.14.2
v1.14.3
v1.14.4
v1.14.5
v1.14.6
v1.14.7
v1.15.0
v1.15.0-dev
v1.15.0-rc1
v1.15.0-rc2
v1.15.0-rc3
v1.15.1
v1.15.10
v1.15.11
v1.15.2
v1.15.3
v1.15.4
v1.15.5
v1.15.6
v1.15.7
v1.15.8
v1.15.9
v1.16.0
v1.16.0-dev
v1.16.0-rc1
v1.16.1
v1.16.2
v1.16.3
v1.16.4
v1.16.5
v1.16.6
v1.16.7
v1.16.8
v1.16.9
v1.17.0
v1.17.0-dev
v1.17.0-rc1
v1.17.0-rc2
v1.17.1
v1.17.2
v1.17.3
v1.17.4
v1.18.0
v1.18.0-dev
v1.18.0-rc0
v1.18.0-rc1
v1.18.1
v1.18.2
v1.18.3
v1.18.4
v1.18.5
v1.19.0
v1.19.0-dev
v1.19.0-rc0
v1.19.0-rc1
v1.19.1
v1.19.2
v1.19.3
v1.19.4
v1.2.0
v1.2.0-rc1
v1.2.0-rc2
v1.2.0-rc3
v1.2.1
v1.2.2
v1.2.3
v1.20.0
v1.20.0-dev
v1.20.0-rc0
v1.20.0-rc1
v1.20.0-rc2
v1.20.1
v1.20.2
v1.20.3
v1.20.4
v1.20.5
v1.20.6
v1.21.0
v1.21.0-dev
v1.21.0-rc0
v1.21.0-rc1
v1.21.0-rc2
v1.21.1
v1.21.10
v1.21.11
v1.21.2
v1.21.3
v1.21.4
v1.21.5
v1.21.6
v1.21.7
v1.21.8
v1.21.9
v1.22.0
v1.22.0-dev
v1.22.0-rc0
v1.22.0-rc1
v1.22.1
v1.22.2
v1.22.3
v1.23.0-dev
v1.3.0
v1.3.0-rc1
v1.3.0-rc2
v1.3.1
v1.3.2
v1.3.3
v1.4.0
v1.4.0-rc1
v1.4.0-rc2
v1.4.0-rc3
v1.4.1
v1.4.2
v1.4.3
v1.5.0
v1.5.0-dev
v1.5.0-rc1
v1.5.0-rc2
v1.5.1
v1.5.2
v1.5.3
v1.6.0
v1.6.0-dev
v1.6.0-rc1
v1.6.0-rc2
v1.6.1
v1.6.2
v1.6.3
v1.6.4
v1.7.0
v1.7.0-dev
v1.7.0-rc1
v1.7.0-rc2
v1.7.0-rc3
v1.7.1
v1.7.2
v1.7.3
v1.7.4
v1.7.5
v1.7.6
v1.8.0
v1.8.0-rc1
v1.8.0-rc2
v1.8.0-rc3
v1.8.1
v1.8.2
v1.8.3
v1.9.0
v1.9.0-dev
v1.9.0-rc1
v1.9.0-rc2
v1.9.1
v1.9.2
v1.9.3
v1.9.4
v1.9.5
v1.9.6
${ noResults }
6 Commits (fe829915475cadd0f6285a30d629772920e8bf32)
| Author | SHA1 | Message | Date |
|---|---|---|---|
|
|
838db2f891
|
Convert to url auth to header auth in tests (#28484)
Related #28390 |
11 months ago |
|
|
da50be7360
|
Replace 'userxx' with 'orgxx' in all test files when the user type is org (#27052)
Currently 'userxx' and 'orgxx' are both used as username in test files when the user type is org, which is confusing. This PR replaces all 'userxx' with 'orgxx' when the user type is org(`user.type==1`). Some non-trivial changes 1. Rename `user3` dir to `org3` in `tests/git-repositories-meta` 2. Change `end` in `issue reference` because 'org3' is one char shorter than 'user3' 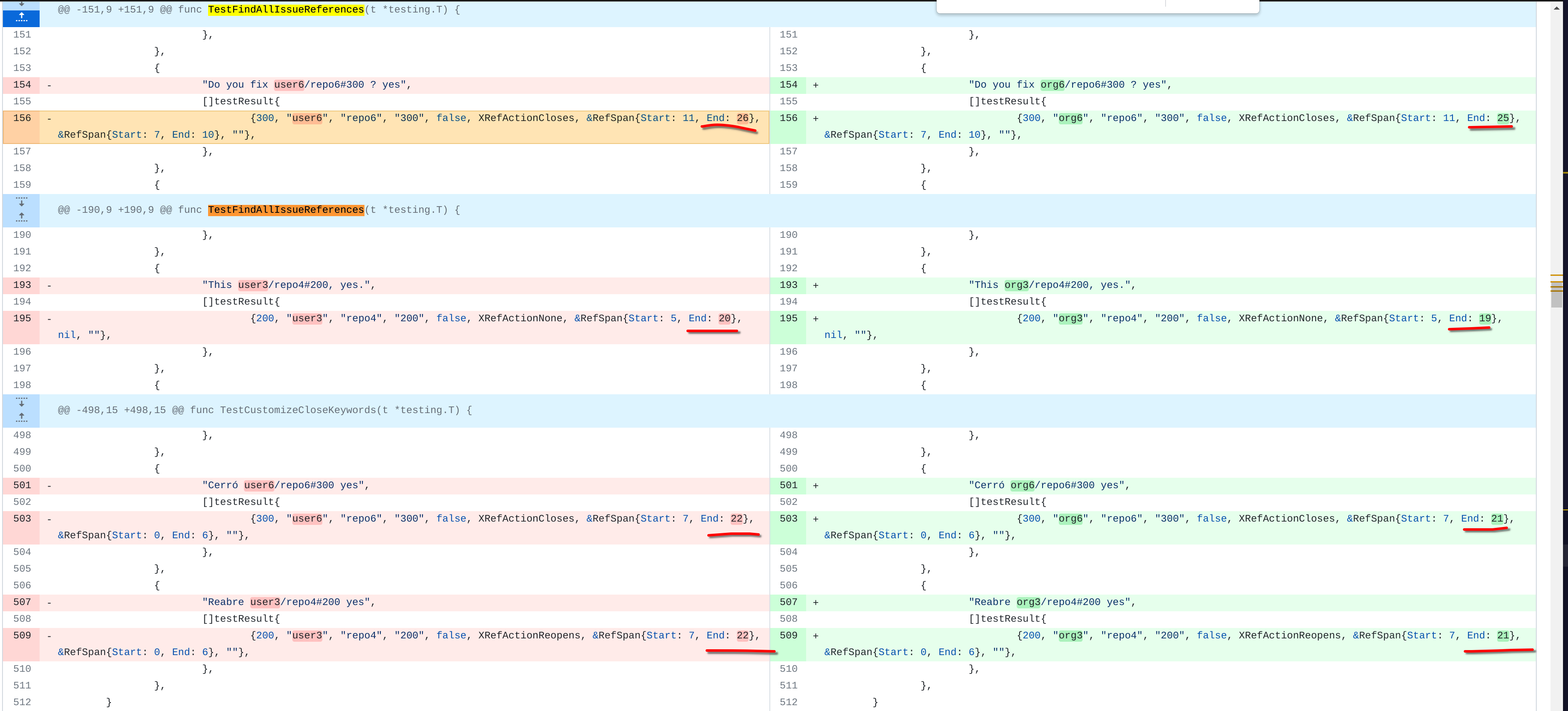 3. Change the search result number of `user/repo2` because `user3/repo21` can't be searched now 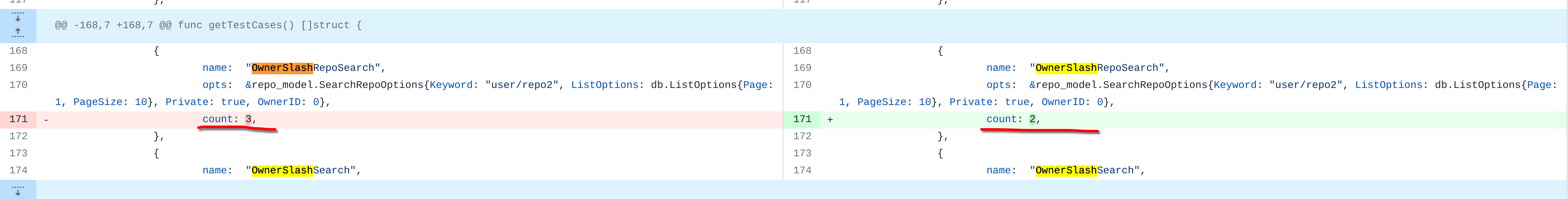 4. Change the first org name getting from API because the result is ordered by alphabet asc and now `org 17` is before `org25`  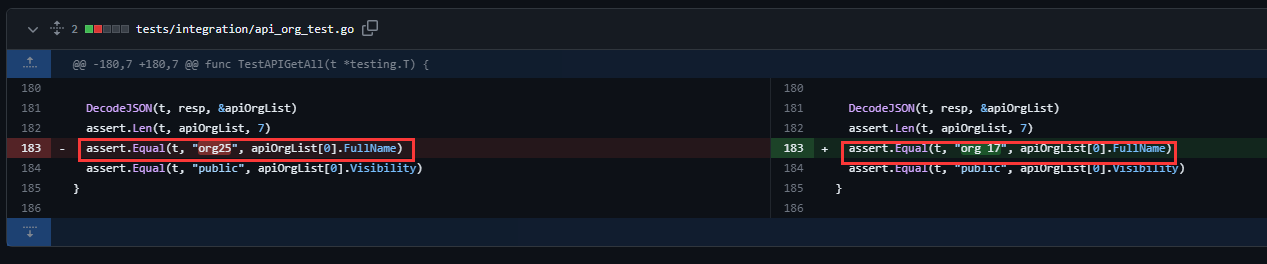 Other modifications are just find all and replace all. Unit tests with SQLite are all passed. --------- Co-authored-by: caicandong <1290147055@qq.com> |
1 year ago |
|
|
ea385f5d39
|
Fix API leaking Usermail if not logged in (#25097)
The API should only return the real Mail of a User, if the caller is logged in. The check do to this don't work. This PR fixes this. This not really a security issue, but can lead to Spam. --------- Co-authored-by: silverwind <me@silverwind.io> |
1 year ago |
|
|
18de83b2a3
|
Redesign Scoped Access Tokens (#24767)
## Changes
- Adds the following high level access scopes, each with `read` and
`write` levels:
- `activitypub`
- `admin` (hidden if user is not a site admin)
- `misc`
- `notification`
- `organization`
- `package`
- `issue`
- `repository`
- `user`
- Adds new middleware function `tokenRequiresScopes()` in addition to
`reqToken()`
- `tokenRequiresScopes()` is used for each high-level api section
- _if_ a scoped token is present, checks that the required scope is
included based on the section and HTTP method
- `reqToken()` is used for individual routes
- checks that required authentication is present (but does not check
scope levels as this will already have been handled by
`tokenRequiresScopes()`
- Adds migration to convert old scoped access tokens to the new set of
scopes
- Updates the user interface for scope selection
### User interface example
<img width="903" alt="Screen Shot 2023-05-31 at 1 56 55 PM"
src="https://github.com/go-gitea/gitea/assets/23248839/654766ec-2143-4f59-9037-3b51600e32f3">
<img width="917" alt="Screen Shot 2023-05-31 at 1 56 43 PM"
src="https://github.com/go-gitea/gitea/assets/23248839/1ad64081-012c-4a73-b393-66b30352654c">
## tokenRequiresScopes Design Decision
- `tokenRequiresScopes()` was added to more reliably cover api routes.
For an incoming request, this function uses the given scope category
(say `AccessTokenScopeCategoryOrganization`) and the HTTP method (say
`DELETE`) and verifies that any scoped tokens in use include
`delete:organization`.
- `reqToken()` is used to enforce auth for individual routes that
require it. If a scoped token is not present for a request,
`tokenRequiresScopes()` will not return an error
## TODO
- [x] Alphabetize scope categories
- [x] Change 'public repos only' to a radio button (private vs public).
Also expand this to organizations
- [X] Disable token creation if no scopes selected. Alternatively, show
warning
- [x] `reqToken()` is missing from many `POST/DELETE` routes in the api.
`tokenRequiresScopes()` only checks that a given token has the correct
scope, `reqToken()` must be used to check that a token (or some other
auth) is present.
- _This should be addressed in this PR_
- [x] The migration should be reviewed very carefully in order to
minimize access changes to existing user tokens.
- _This should be addressed in this PR_
- [x] Link to api to swagger documentation, clarify what
read/write/delete levels correspond to
- [x] Review cases where more than one scope is needed as this directly
deviates from the api definition.
- _This should be addressed in this PR_
- For example:
```go
m.Group("/users/{username}/orgs", func() {
m.Get("", reqToken(), org.ListUserOrgs)
m.Get("/{org}/permissions", reqToken(), org.GetUserOrgsPermissions)
}, tokenRequiresScopes(auth_model.AccessTokenScopeCategoryUser,
auth_model.AccessTokenScopeCategoryOrganization),
context_service.UserAssignmentAPI())
```
## Future improvements
- [ ] Add required scopes to swagger documentation
- [ ] Redesign `reqToken()` to be opt-out rather than opt-in
- [ ] Subdivide scopes like `repository`
- [ ] Once a token is created, if it has no scopes, we should display
text instead of an empty bullet point
- [ ] If the 'public repos only' option is selected, should read
categories be selected by default
Closes #24501
Closes #24799
Co-authored-by: Jonathan Tran <jon@allspice.io>
Co-authored-by: Kyle D <kdumontnu@gmail.com>
Co-authored-by: silverwind <me@silverwind.io>
|
1 year ago |
|
|
e81ccc406b
|
Implement FSFE REUSE for golang files (#21840)
Change all license headers to comply with REUSE specification. Fix #16132 Co-authored-by: flynnnnnnnnnn <flynnnnnnnnnn@github> Co-authored-by: John Olheiser <john.olheiser@gmail.com> |
2 years ago |
|
|
a577214760
|
Add some api integration tests (#18872)
depends on #18871 Added some api integration tests to help testing of #18798. Co-authored-by: Lunny Xiao <xiaolunwen@gmail.com> Co-authored-by: wxiaoguang <wxiaoguang@gmail.com> Co-authored-by: zeripath <art27@cantab.net> Co-authored-by: techknowlogick <techknowlogick@gitea.io> |
2 years ago |